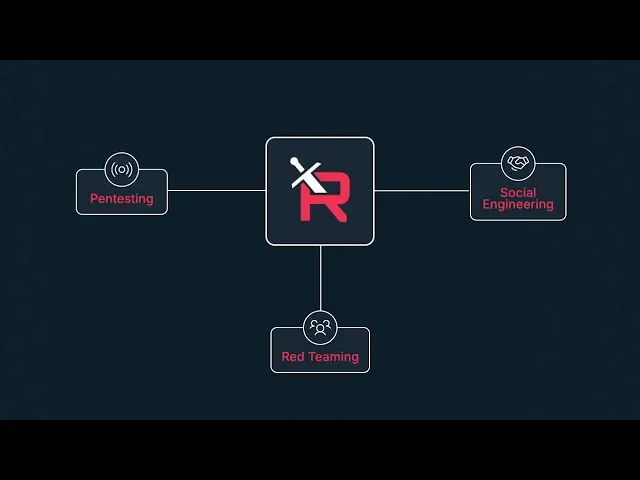
Complete manual pentests in days not months
Comprehensive coverage across web, network, API, and cloud systems
Manual testing by certified experts — no automated scanners
Audit-ready reports for SOC 2, HIPAA, PCI, ISO 27001, and more.
Real-time collaboration through our award-winning PTaaS platform
4.8-star average rating on Capterra and G2
Join 750+ companies who've hardened their security with Red Sentry
We go beyond checkbox pentesting. Our testers replicate real-world attack scenarios to uncover the vulnerabilities automated tools miss — giving your team the clarity and confidence to fix issues fast.
Comprehensive security testing for modern enterprise infrastructure.
Save time, avoid false positives, truly operationalize security, and manage costs.
“The Red Sentry team was able to deliver quick, but thorough, results for my business. Their responsiveness and findings were critical in closing a new client engagement. I am looking forward to working with them in the future.”
Craig Serold | Partner
"Complete satisfaction. Nothing less. From concept to conclusion, you are in great hands throughout the entire process."
Douglas G. | CEO
“Seamless, constructive, efficient. They are always quick to respond to customers and very easy to work with regarding scheduling.”
Ryan M. | Director of Sales
“Very good. They provided recognized credibility and gave us a clean bill of health on issues we had resolved.”
David N. | Leader of Client Delight
Get actionable results prioritized by severity, so you know where to act first.
Other Pentest Solutions
Tool Usage: Use scanners in lieu of pentesters
Time to Launch: Weeks to Months
Price: High
(excessive fluff hours charged)
Support: Medium
False Positive Rate: Medium
Customer Satisfaction: Medium
Red Sentry
Tool Usage: Led by expert pentesters and tools only used to augment skill
Time to Launch: < 7 days
Price: Most Competitive
(Ask about Price Matching)
Support: High with dedicated PMs and Team Leads
False Positive Rate: Low
Customer Satisfaction: High
Get a fast, no-pressure scoping call to see how our cybersecurity testing process works.
What is cybersecurity penetration testing?
Cybersecurity penetration testing simulates cyberattacks to identify vulnerabilities in your organization’s systems, networks, and applications. It helps companies strengthen defenses, meet compliance requirements, and reduce the risk of breaches.
What is the difference between a vulnerability scan and a penetration test?
A vulnerability scan is automated and flags potential weaknesses. A penetration test is human-led and actively exploits vulnerabilities to show the real business impact and risk.
How do you handle testing without disrupting uptime for our SaaS platform?
We coordinate closely with your engineering team to plan scope and timing. Our testing methods are designed to be non-disruptive, so your customers experience no downtime or performance issues.
What is network penetration testing?
Network penetration testing simulates attacks on your internal and external networks to uncover misconfigurations, weak passwords, and other risks that could allow attackers to gain unauthorized access.
What is web application penetration testing?
Web application penetration testing simulates attacks on websites and web apps to identify vulnerabilities such as SQL injection, cross-site scripting (XSS), and authentication flaws.
What are red team services?
Red team services simulate full-scale cyberattacks using advanced tactics to test how well your organization can detect, respond, and recover from threats. Unlike standard penetration testing, red team engagements focus on real-world attack scenarios.
What does a cloud penetration test cover?
A cloud penetration test assesses environments like AWS, Azure, and Google Cloud, identifying risks such as misconfigured IAM policies, insecure storage, and weak security rules that could expose sensitive data.
What is web application penetration testing?
Web application penetration testing simulates cyberattacks on websites and SaaS apps to find vulnerabilities like SQL injection, cross-site scripting (XSS), and authentication flaws that could expose sensitive data.
What is Red Sentry’s hybrid approach and how does it benefit me?
Our hybrid approach combines the efficiency of automated tools with the expertise of human testers. This ensures faster, more thorough results while eliminating false positives and uncovering complex vulnerabilities.
What can I expect from a Red Sentry penetration test report?
Our reports are clear, actionable, and audit-ready. They include prioritized vulnerabilities, remediation guidance, and at least one retest to verify fixes.
What is SOC 2 penetration testing?
SOC 2 penetration testing helps organizations meet SOC 2 compliance by simulating attacks to validate that systems and controls protect sensitive customer data.
How is pricing determined for Red Sentry’s penetration testing services?
Pricing depends on the size and complexity of the environment. We offer transparent, customized pricing with no hidden fees, determined during an initial scoping call.








